Build Your Personal Cybersecurity Toolkit: Step-by-Step
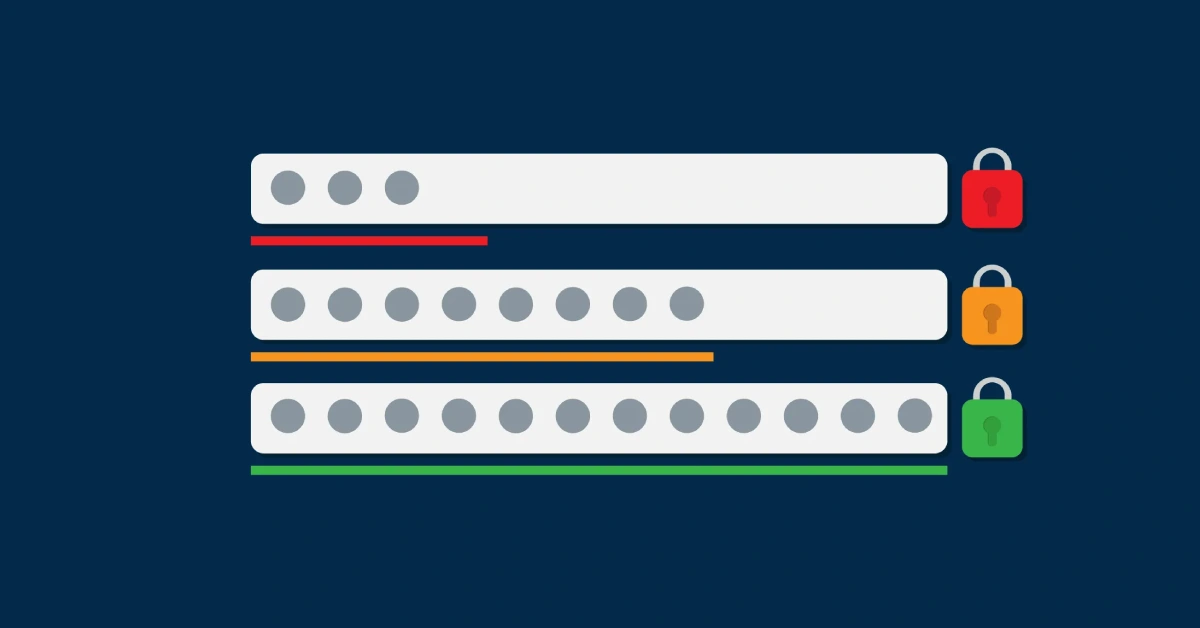
A personal cybersecurity toolkit includes five core elements: a password manager for unique passwords, two-factor authentication for account security, phishing detection skills for email safety, identity controls for privacy protection, and secure backup systems for data recovery. These tools work together to protect your digital life from common cyber threats while remaining simple enough for … Read more